Every business organization must have an effective and robust cybersecurity strategy to prevent malicious actors (or hackers) from trying to barge into your organization’s network periphery. Your best move is to integrate cybersecurity into your business culture – ‘build security in.’ Having a proactive approach towards cybersecurity is the need of the hour.
Cybersecurity threats have become one of the worst nuisances in these technologically advanced times. Businesses worldwide employ excellent cybersecurity strategies, tools, and techniques to thwart malicious cyberattacks like phishing, ransomware, and other forms of data breaches. Despite these strategies, malicious actors infiltrate enterprise networks by inventing novel methods, making it imperative for businesses to keep an eye on their cybersecurity posture continually and keep it top-notch at all times.
Cybersecurity Statistics That Confirm The Grim Cybersecurity Posture Of Organizations
Organizations have varying criteria and approaches when reporting cyber incidents or data breaches. Each business has its research methodology based on its internal systems data, customer monitoring data, or data supplied by cybercrime victims. Here is an overall industry perspective of cybersecurity statistics for 20201.
- Business Email Compromise or Account Email Compromise scams have been the most common in 2020. Such scams have cost business organizations millions of dollars globally. It has become the most lucrative attack vector in 2020.
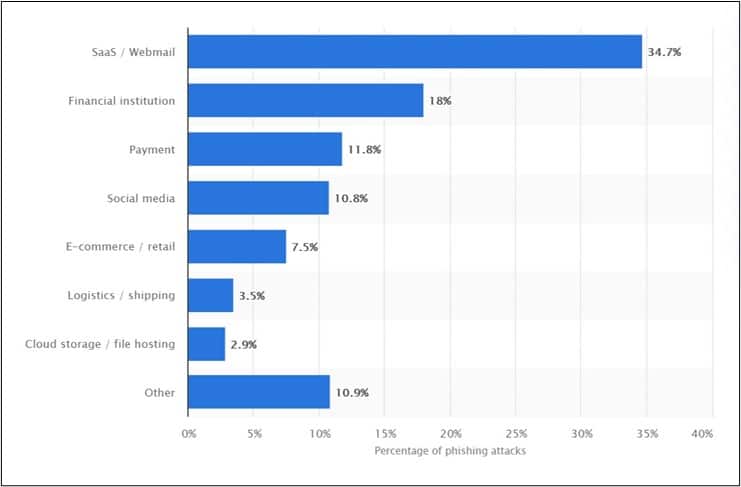
- Phishing attacks have witnessed a continuous increase every quarter since 2017, with the second quarter of 2020 accounting for the highest in many years.
- Some of the top corporate entities targeted for brand impersonations include Apple, Netflix, and Yahoo.
- Online payment fraud has also proved to be a leading contributor to cybersecurity incidents in 2020. Market forecasts say that the emerging threat could cost the eCommerce industry at least $25 billion annually by 20242.
- An AT&T survey shows that 73% of the world’s leading organizations consider strong cybersecurity as a significant contributor to the business’ success.
While the statistics listed out seem chilling, below are some recent data breaches in different industrial sectors in 2020.
Recent Eye-Opening Breaches
The year 2020 has seen numerous data breaches of different kinds happening all over the world. It has infected almost every industrial sector. Here are some of the recent eye-opening breaches3 worth consideration.
-
Marriott Data Leak
The Marriott Data Leak is a classic example wherein malicious actors used two employees’ login credentials to siphon out the information of about nearly 5.2 million Marriott guests. The data included personal information, such as contact details, gender, birthdates, and airline loyalty program data. Though it is not specific about how malicious actors obtained employee credentials, it is suspected that credential stuffing and phishing must be the methods employed.
-
Antheus Tecnologia Biometric Data Breach
Antheus Tecnologia, a Brazilian biometrics solutions provider, suffered a data breach in 2020. A pro bono team of security researchers revealed that the organization left sensitive info, including data from 76,000 fingerprints, exposed on an unsecured server. Though the server did not store the digital scans of fingerprints, it had the binary code that malicious actors could use to recreate them. The breach happened because the organization neglected to encrypt the database or use a password to protect it.
-
EasyJet Data Breach
EasyJet, a low-cost airliner, reported a massive data leak when a highly sophisticated malicious actor stole nine million users’ data. This breach has far-reaching implications as it exposed personal details like email addresses, names, credit card information, travel records, etc.
The above were examples of three different kinds of data breaches in 2020. No one can wish these breaches away as long as businesses and individuals keep making mistakes in cybersecurity.
Critical Cybersecurity Challenge Facing Organizations Today
The crucial aspect of cybersecurity is to stay a couple of steps ahead of the malicious actors and take preventive action before they start exploiting the system. While they keep getting smarter by the day, organizations have to be extra-vigilant in protecting user privacy. In this digital era, news abounds regarding cyberattacks like phishing, IoT-based breaches, ransomware, and other vulnerability exploits.
Here are some of the critical cybersecurity challenges that organizations the world over encounter daily.
-
Technical Skills Gap In Cyberspace
Businesses globally face a common challenge of a gap in technical skills. Research shows that nearly 48% of organizations cannot carry out basic cybersecurity tasks like storing data securely or setting up firewalls. The same study shows that almost 30% of these business entities lack advanced cybersecurity skills like forensics and pen-testing.
A NY Times report forecasts that there will be nearly 3.5 million unfilled cybersecurity jobs in 2021. It indicates that organizations’ most significant challenge is the inability to provide cybersecurity professionals at the same speed at which vulnerabilities increase in the enterprise information network.
It entails that businesses should concentrate on bridging the gap by training their existing staff to prevent cyberattacks.
-
The Parallel Role Of AI-ML In Cyberattack And Prevention
Artificial Intelligence and Machine Learning (AI-ML) has proved beneficial to almost every industry. A straightforward example is the biometric login facility that has proved helpful to businesses worldwide by preventing illegal access to unauthorized personnel.
AI allows businesses to learn the anomalies in behavioral patterns and use them as a defensive tool. Simultaneously, the same techniques can prove useful to malicious actors to learn how to launch cyberattacks with sophisticated tools and methods leveraging AI-ML.
-
Constant Ransomware Threats
Another global cyber threat that has been making headlines is ransomware. It is the fastest-growing cyberattack in this technological era. Malicious actors use ransomware to encrypt files and block user access to the enterprise network. Generally, they use tactics like phishing to introduce ransomware into the network.
Blocking access to critical data cripples the business, following which the criminals demand money to offer a solution. The ransom depends on the size of the organization and the criticality of the data.
Ransomware results in business entities losing on both the productivity and financial fronts. Besides, organizations incur additional IT and legal costs.
-
Cloud Computing And Security Risks
Storing data in legacy data centers cause businesses to incur massive costs. Besides, there is not enough flexibility available to organizations in the option. Therefore, enterprises are moving their sensitive data to the cloud. However, they should exercise caution when it comes to configuring data. Adequate security measures must be in place, lest they fall into a trap.
Securing the organization’s infrastructure and data from theft over the cloud is a business’s responsibility. They can employ various security measures such as VPN, MFA, and firewalls to safeguard data and prevent external and internal threats.
-
Internet Of Things (IoT) And Emerging Threats
Today, businesses adopt IoT for performing various functions, including manufacturing. IoT requires network support and communication for its proper functioning. However, it exposes the enterprise to security threats like DDoS and ransomware. Malicious actors can exploit vulnerabilities in the IoT infrastructure and execute cyberattacks. Organizations can train SOC (Security Operations Center) employees around IoT risks and install SIEM (Security Incident and Event Management) to manage thousands of IoT devices and protect the organization against threats originating from IoT usage.
How Can Organizations Improve Their Cybersecurity Posture?
Here are some ways using which organizations can improve their cybersecurity posture5 and mitigate cyber threats.
No hardware system is ever perfect. As technology improves, existing systems become outdated. Malicious actors keep looking for gaps to exploit. Hardware manufacturers and software developers keep releasing regular updates that help organizations enhance security levels to protect against cyber threats.
Businesses should typically update their firmware at least once a year. Outdated hardware does not guarantee security, and malicious actors can easily infiltrate vulnerable networks. Updating firmware periodically helps to fix existing vulnerabilities and bugs. Though it costs additional money and effort, it is worth every dollar spent keeping system software and applications updated.
-
Use Of WPA2 (Wi-Fi Protected Access II)
Business networks should use a reliable and encrypted protocol for passwords on the router. WPA (Wi-Fi Protected Access) is one of the most advanced protocols in use today. Wi-Fi Protected Access II (WPA2) has much more robust security and is easier to configure than its predecessors. Organizations must ensure that the relevant security protocol is appropriately configured in the enterprise network routers.
-
Disable DHCP (Dynamic Host Configuration Protocols)
One of the crucial ways to maintain a secure Wi-Fi network is to have DHCP (Dynamic Host Configuration Protocols). It defines which IP addresses a network should have. Limiting the number of IPs assigned by DHCP or even disabling it can make the enterprise information network safer. However, it requires the IP address to be set manually for every device connected to the Wi-Fi.
-
Using VPN Can Secure The Wi-Fi Network
In these days of WFH (Work From Home), employees use their home network for accessing the office network. However, external networks do not have the same security levels as the enterprise’s primary network. Hence, it is ideal for businesses to use VPNs (Virtual Private Network) to ensure that employees do not compromise with sensitive data. VPNs feature a built-in kill switch that disconnects the enterprise network hardware whenever the protected connection is lost. Thus, it keeps data safe from unexpected data leakage.
-
Disable By Default File Sharing
Businesses must disable default file-sharing to safeguard data and implement control measures to enable it on a ‘need-to-know’ basis. Enabling file sharing on all devices means that data will be accessible to all users using the Wi-Fi connection. One should allow file sharing on an organization’s file servers alone.
-
Use SSL Certificates
Using SSL certificates allows encrypted communication links between a client machine and the enterprise network web server. It makes online transactions secure. SSL helps affirm user identity and protect enterprise data, and complying with PCI-DSS and relevant regulatory requirements.
-
Change The Name Of The Enterprise Network
Internet service providers assign default names for the organization’s network for the subscription. It generally contains the router model number. Though a user sets specific passwords, using the original name can be insecure. Malicious actors can find the necessary documentation to gain access to the network. Hence, it is advisable to change the name of the network.
-
Use Strong Passwords And Keep Changing Them At Intervals
A significant number of cyber-attacks occur because users compromise with their credentials. It could be by way of using simple passwords that are easy for malicious actors to guess. Hence, the network and all its users should use robust passwords and change them at frequent intervals.
-
Delete Unused Accounts That Malicious Actors Can Exploit
Generally, malicious actors use unused and dormant accounts to gain access to an organization’s network. Such instances can happen if the business has gone through multiple employees or transitioned to a different system.
Organizations should clean up such accounts and deactivate them. It prevents malicious actors from accessing and misusing them to introduce malware into the network.
-
Restrict Admin Access To A Chosen Few
Business entities sometimes give users full access to their workstations to install software solutions or change settings. It can offer some convenience but can prove harmful. Unsuspecting users could download a malicious attachment or click on malicious links that could compromise security.
The solution is to restrict Admin access to authorized users alone, primarily those having the technical capability to carry out such changes securely to the enterprise network. It also helps the organization exercise better control over employees’ resource usage.
-
Train And Educate Employees In Matters Concerning Cybersecurity
Malicious actors use phishing or ransomware to target vulnerable employees and infiltrate the organization’s information network. Businesses should train and educate their employees on basic cyber hygiene, such as:
- Not to open unsolicited emails or click on doubtful links that could compromise critical data.
- Using a strong password and following the password best practices.
- Be able to report the security incidents or suspicious activities to the right authorities and write it down if necessary.
-
Employ Multifactor Authentication
Enterprises should employ multifactor authentication (MFA) to configure users’ identities with two or more access credentials. MFA enables a higher security level as it makes it challenging for malicious actors to access a network.
- MFA is one of the most effective prevention methods against unauthorized access.
- Provides an extra layer of security to sensitive and critical data.
- MFA works as an attempted attack alert mechanism to an employee if cyber adversaries try to use it.
-
Secure The Enterprise Information Networks
Enterprise information networks can safeguard their internet connections by using firewalls and robust antivirus solutions. Though no product or service guarantees 100% security, a firewall controls the network’s incoming and outgoing data. Threat actors find it challenging to infiltrate a network by breaking additional security layers.
-
Have An Effective Backup Policy
An effective backup cannot prevent any data breach but can help clean it up. Today, ransomware is a growing threat to the industry. The lack of a backup can result in a ransomware attack and risk losing access to the information network files. Having a regular backup is a proactive step towards having a continuity plan for the organization. However, organizations must also regularly test if it can be restored if necessary.
-
Be Abreast Of The Latest Happenings On The Cybersecurity Front
The key to preventing cyberattacks is to be proactive. Business entities should keep updated with the latest cybersecurity threats and implement the most advanced safeguards capable of thwarting them. It is better to be prepared rather than be caught unawares by malicious actors.
Final Thoughts
Today, it is impossible for a business to function without being online. However, it comes with its share of problems. Malicious actors are forever on the prowl looking out for vulnerabilities they could exploit. Hence, business organizations should invest in cybersecurity and follow the best strategies to prevent cyberattacks. Besides, employees should exercise vigilance and be aware of all cyber risks as they are the first line of defense against cyberattacks.
References
-
Casey Crane, The Definitive Cybersecurity Statistics Guide for 2020, May 15, 2020, Security Boulevard, https://securityboulevard.com/2020/05/the-definitive-cyber-security-statistics-guide-for-2020/
-
Juniper Research, Ecommerce Losses to Online Payment Fraud to Exceed $25 Billion Annually by 2024, March 30, 2020, https://www.juniperresearch.com/press/press-releases/ecommerce-losses-to-online-payment-fraud-to-exceed
-
Martin Gontovnikas, The 11 Biggest Data Breaches of 2020 (So Far), Auth0 – Blog, https://auth0.com/blog/the-11-biggest-data-breaches-of-2020-so-far/
-
Ruchika Tyagi, Cybersecurity Challenges In 2020 And How To Tackle Them, May 27, 2020, Teceze, https://www.teceze.com/cybersecurity-challenges-in-2020-and-how-to-tackle-them/
-
Chelsea Segal, 6 Simple Tips to Increase Your Small Business Security Using Inexpensive Cybersecurity Measures, Cox BLUE, https://www.coxblue.com/6-simple-tips-to-increase-your-small-business-security-using-inexpensive-cybersecurity-measures/
-
Dainan Gilmore, 9 Ways to Make your Company Network Secure, April 23, 2019, TDWI, https://tdwi.org/articles/2019/04/23/dwt-all-9-ways-to-make-your-company-network-secure.aspx

